RBAC Tooling
Rakkess
Have you ever wondered what access rights you have on a provided kubernetes cluster? For single resources you can use kubectl auth can-i list deployments, but maybe you are looking for a complete overview? This is what rakkess is for. It lists access rights for the current user and all server resources.
You can get more details here.
Install Rakkess for your platform
Let’s examine the RBAC for the default Namespace:
rakkess -n default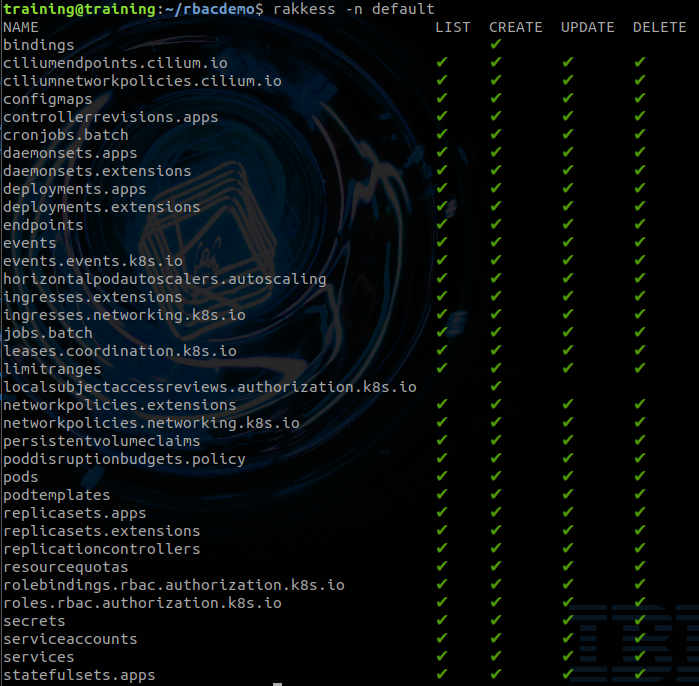
And now the RBAC for the ServiceAccount that we have created earlier:
rakkess --sa service-account-1 -n default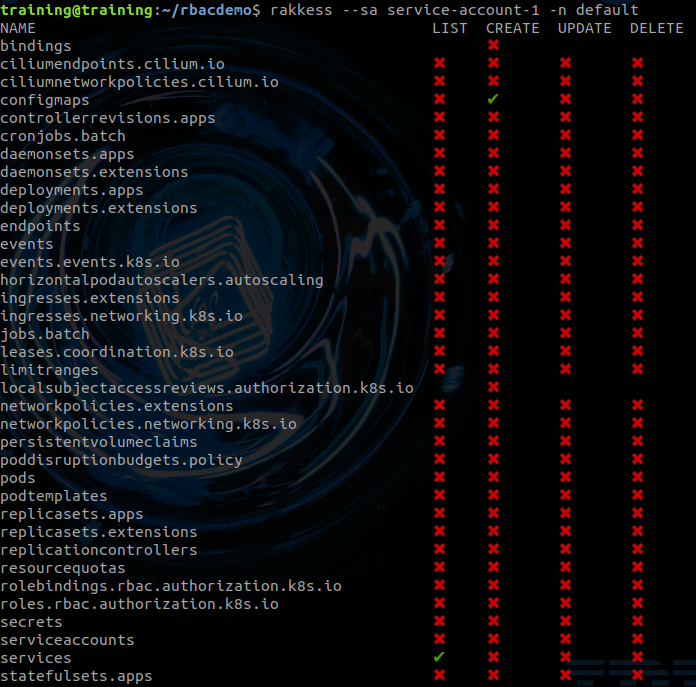
We can see that the
ServiceAccounthas the rights to listServicesand to createConfigMaps. This corresponds to theapi-roleRolethat we have defined earlier:...- apiGroups: [""]resources: ["services"]verbs: ["get", "list"]- apiGroups: [""]resources: ["configmaps"]verbs: ["create"]...
rbac-view
Polaris runs a variety of checks to ensure that Kubernetes pods and controllers are configured using best practices, helping you avoid problems in the future.

You can get more details here.
Install rbac-view
#Linuxwget https://github.com/jasonrichardsmith/rbac-view/releases/download/v0.2.1/rbac-view.v0.2.1.linux.tar.gztar xf rbac-view.v0.2.1.linux.tar.gzchmod +x ./bin/linux/rbac-viewsudo mv -i ./bin/linux/rbac-view $GOPATH/bin/rbac-view#Macwget https://github.com/jasonrichardsmith/rbac-view/releases/download/v0.2.1/rbac-view.v0.2.1.darwin.tar.gzRun the following in your Terminal:
rbac-view> INFO[0000] Getting K8s client> INFO[0000] serving RBAC View and http://localhost:8800Open the followin URL in your browser: http://localhost:8800
Rbac-view will then run some initialization which may take some time.
```output> INFO[0000] Getting K8s client> INFO[0000] serving RBAC View and http://localhost:8800...> INFO[0039] Building full matrix for json> INFO[0039] Building Matrix for Roles> INFO[0039] Retrieving RoleBindings> INFO[0039] Building Matrix for ClusterRoles> INFO[0039] Retrieving ClusterRoleBindings
Enter
clusterin theSearchRolesfield and examine thecluster-adminRole. The*means that it has all access rights to all ressources with all verbs.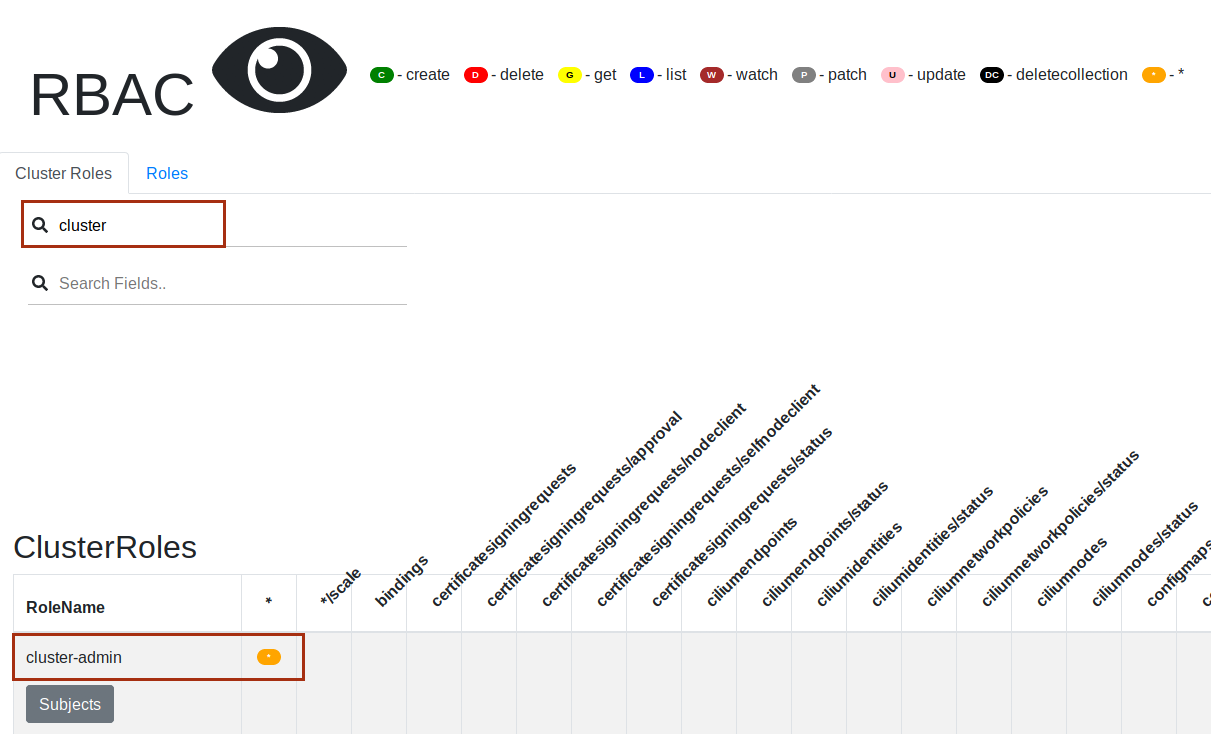
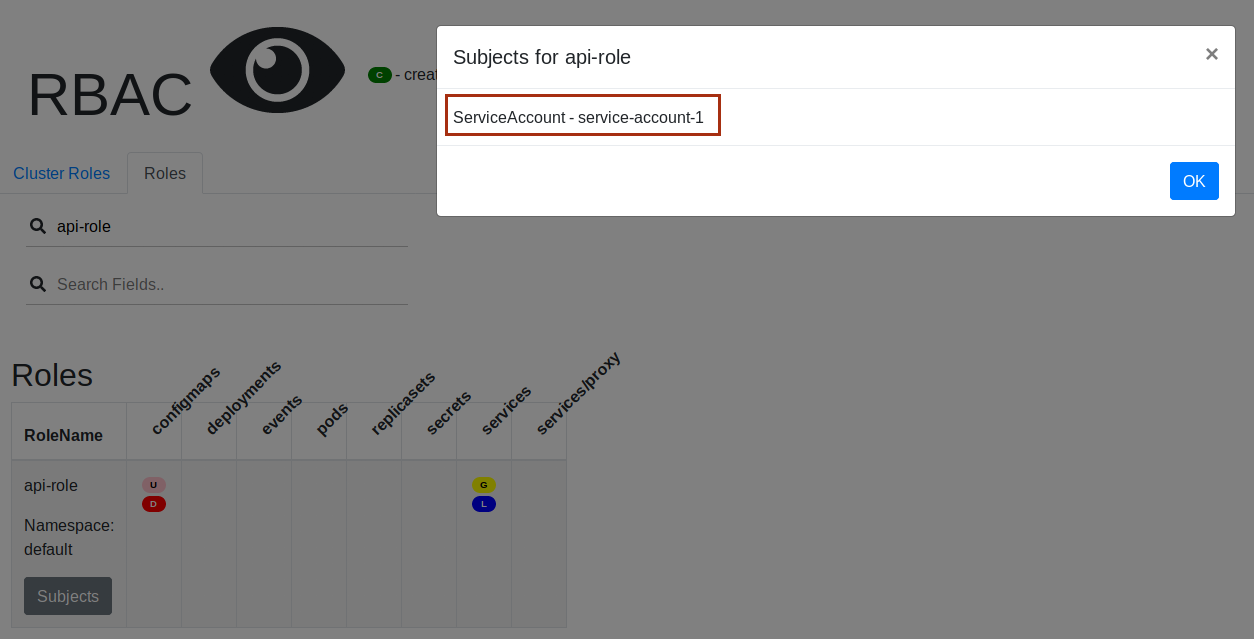
Switch to the Roles tab and enter
api-rolein theSearchRolesfield and examine it. We can see the access rights previously discussed, notablygetandlistrights toServices.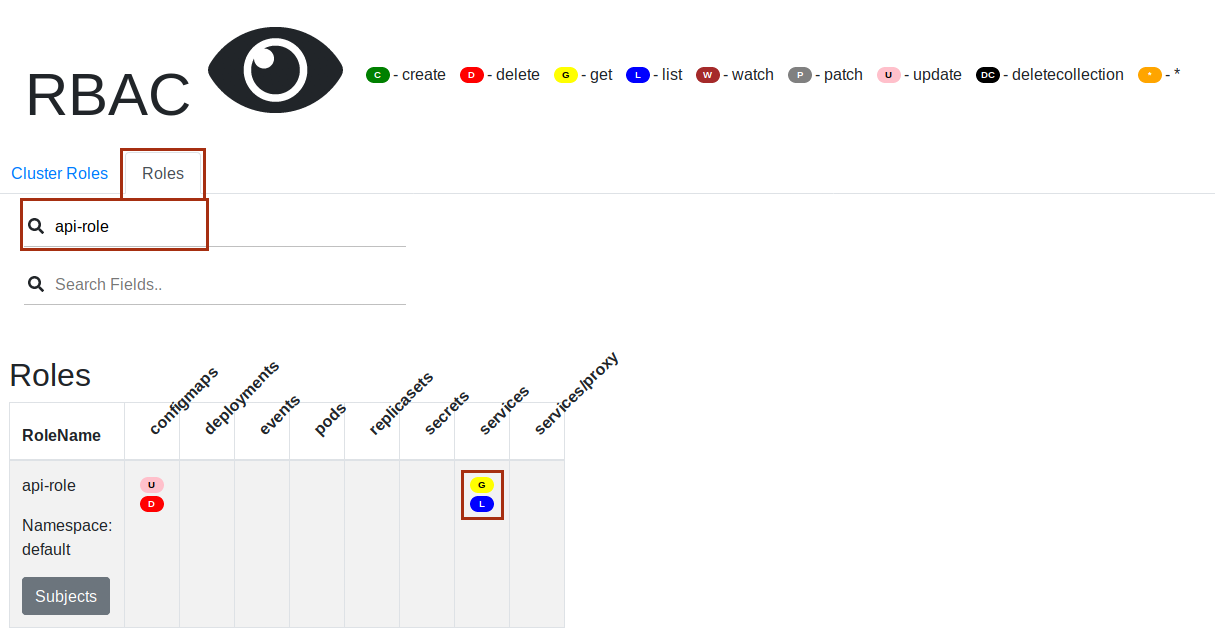
When you click on the Subjects button you will get the list of Subjects for this
Role. In this cas we can see theServiceAccountservice-account-1that is a subject of the Role.